Last month our GM International Elsa Madrolle provided a 2-part overview of the 4 AML Lenses with which to view the FATF Travel Rule platforms through.
On 26 March, Sygna Bridge project manager Vince Lee built on this with a strong examination of the technical requirements that Travel Rule solutions should meet, using Sygna Bridge as a reference point for comparison purposes.
Introduction
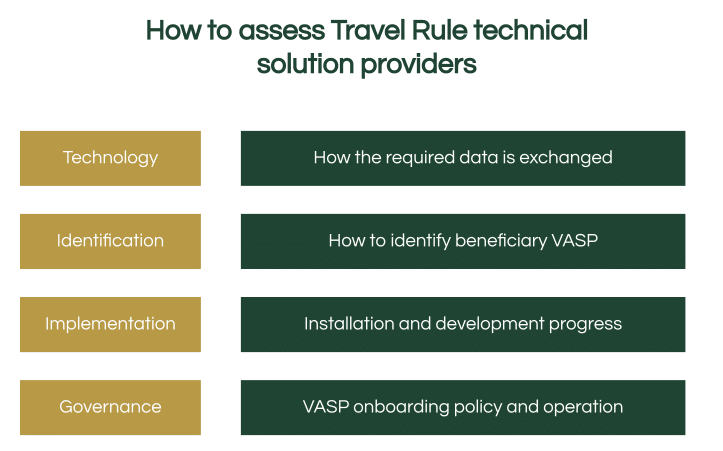
This is the first session of our new educational series on how to choose a Travel Rule solution with the 4 lenses: Technology, Identification, Implementation, and Governance.
- Technology focuses on how the Travel Rule required information is exchanged between different solutions.
- Identification looks at when a transaction request is submitted by the user, how the wallet address is identified as it belongs to which VASP
- Implementation dissects how the software can be installed, and what is each one’s development progress
- Governance covers the VASP onboarding policy, and operations of the network.
This article, which has been adapted from Vince’s presentation, looks at these essential questions:
- How do the existing technologies transfer the information?
- What are the three technology keys to choosing a solution?
- How do the different solutions compare with each other?
- How can Sygna Bridge fulfill the three keys?
View Webinar:
https://www.youtube.com/watch?v=RBtdf1DfOEA
View Slides: https://docs.google.com/presentation/d/1LIjDwlZuXKIZGDaWbEgBhwdhL0Xo38Er9AM_ky9IQNs/edit
Existing Technology
Let’s look at the existing technology, which can be separated into 3 categories:
- 1. Decentralized P2P connections
- 2. Blockchain nodes
- 3. Centralized solutions
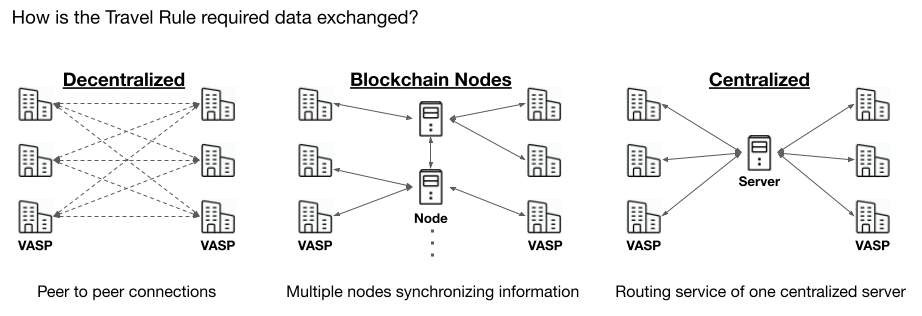
1. With decentralized peer-to-peer connections, each VASP has to establish connections to every VASP in the network to ensure data transfer in the API interface.
2. With blockchain nodes, each VASP can share the encrypted information to a node then the nodes will sync the information with each other so that the destination VASP can get the latest information from the synchronized nodes.
Blockchain nodes are considered half-centralized, half-decentralized, because the information is still relying on a third party to be transferred.
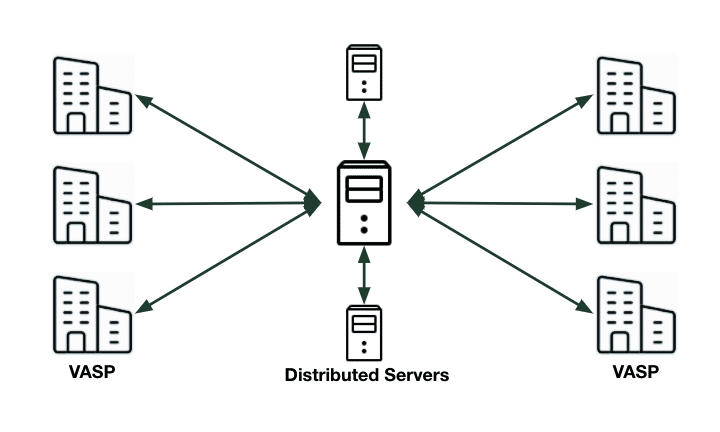
3. A centralized server provides a routing service which is common in the software as a service (SaaS) industry. Each VASP only sends and receives information from one server with the highest efficiency.
3 Keys to identifying the right technology solution
Although the three different types of technologies can help to transfer messages, there are also three different keys that can help you identify the right solution for you.
1) Whitelisting endpoints
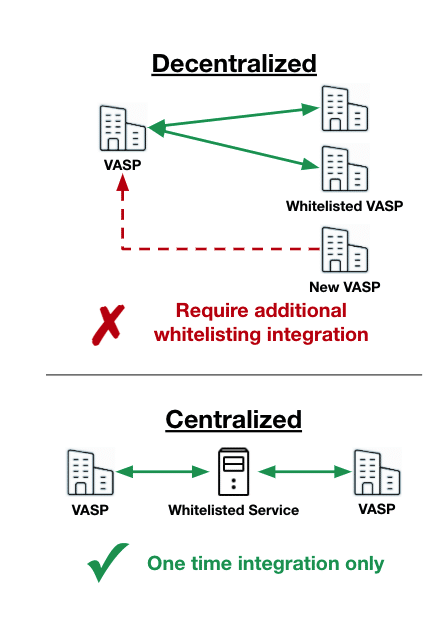
Whitelisting endpoints is important in the financial industry and is widely used by information systems because they care about information security. They want to protect their server or database from external malicious connections so each connection requires whitelist registration.
For example, before a VASP establishes a connection with a new VASP, they have to whitelist the counter-party endpoints such as IP address or API endpoints first.
This protects their service during the data transfer that only whitelisted connections can access the service.
That creates an issue that when every new member enters the network, the existing members have to go through the whitelisting process to onboard the new one.
A centralized solution can make sure the whitelisting process for VASPs only takes place one time because the VASP only connects with the whitelisted centralized service.
2) Data encryption
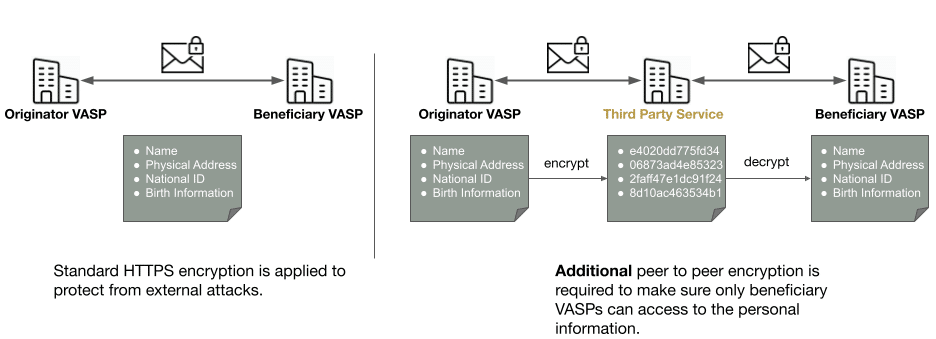
The second key is data encryption. There are two ways of information sharing:
- 1) sending directly or
- 2) sending through a third-party service.
When the information is shared directly to the destination VASP, a standard HTTPS encryption is applied to protect the data from external attacks. This allows only the destination VASPs to see the information inside the encryption.
However, you want to send the information through a third-party service, it requires additional encryptions so that the third party can not access the information but the destination VASP can see the information inside the encryption.
For example, when the originator VASPs want to send the user name and the personal information, they have to encrypt it using the beneficiary VASP public key so that the encrypted information is not accessible to the third party service. After third-party service providers pass the information to beneficiaries VASPs, they can decrypt it using their private key to access the information.
Any centralized or half-centralized technologies will require additional encryption mechanisms to protect information privacy.
3) One-way data exchange
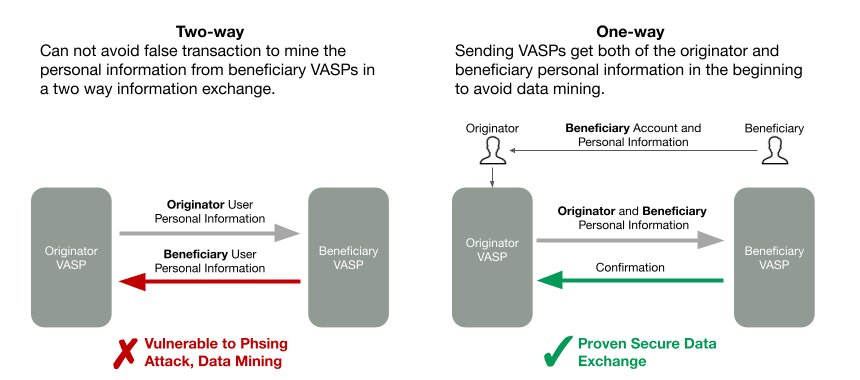
The third key is one-way data exchange, which also revolves around data security, because a traditional two-way information exchange is vulnerable to phishing attacks.
For example, if you and I are two strangers meeting on the street and we want to exchange names, I can self-claim any name, even a fake one, in order for you to reveal your real name in good faith.
This also happens in the information industry where everything is mostly automated and difficult to check with the process that can lead to phishing attacks, or as we call it,data mining.
A better and more foolproof way to exchange information is a one-way data exchange. We will let the originator get the beneficiary’s personal information when they share the account information in the first place. Then that information will be given to the originator VASP so that they can confirm with the beneficiary VASP whether the beneficiary name is correct via an automated API service.
This is a more secure way to exchange information and is widely used in the information industry.
After looking at the three keys in choosing the right Travel Rule solution, let’s discuss the technology of Sygna Bridge’s FATF Travel Rule solution.
The Technology of Sygna Bridge
When our team was designing our Sygna Bridge messaging platform to meet Travel Rule requirements, we committed to three core tenets:
- It needed to be easy to integrate with;
- It needed to possess a fast transfer speed;
- It needed to be flexible to each jurisdiction’s compliance requirements.
By utilizing AWS’ trusted distributed cloud server technology, we built Sygna Bridge to ensure VASPs only need to integrate with us once. The distributed server will deliver the sending message to the assigned destination. The technology can automatically scale up with ease to accommodate up to 100,000 transfers per second.
In our production test in April 2020, the speed for the whole cycle of one messaging transfer was recorded to be as fast as 0.5 seconds.
With the distributed technology, the server and database can be localized in each region to meet each jurisdiction’s compliance and privacy requirements.
3 Key Comparisons: Sygna vs other Messaging Technologies
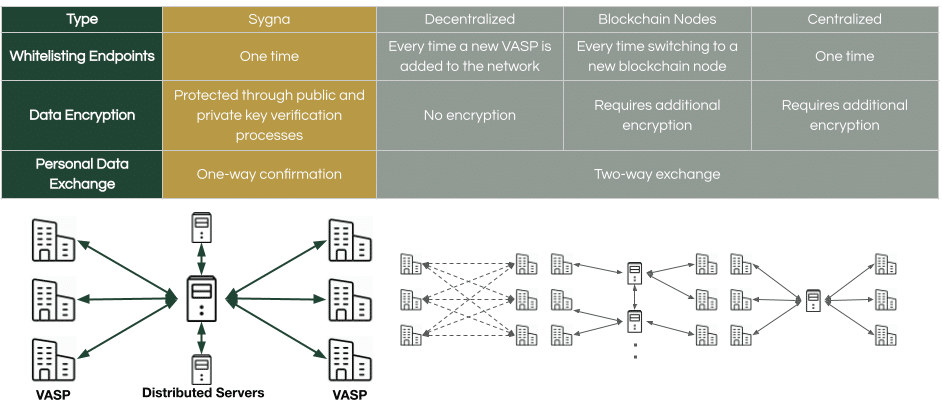
Whitelisting endpoints:
- Centralized technology like Sygna only requires a 1-time integration
- Decentralized technology will require additional integrations.
- Blockchain nodes also require additional integrations when changing to a new node.
Data Encryption:
- Sygna protects personal information through public and private key encryptions.
- When choosing a solution, blockchain nodes and centralized technologies both share the information with a third party which requires extra peer-to-peer encryption. Please pay close attention to that.
Data Exchange:
Sygna is the only solution with the one-way confirmation exchange design, which enhances user privacy with a higher level of data protection.
Comparing Scalability, Security, and Privacy
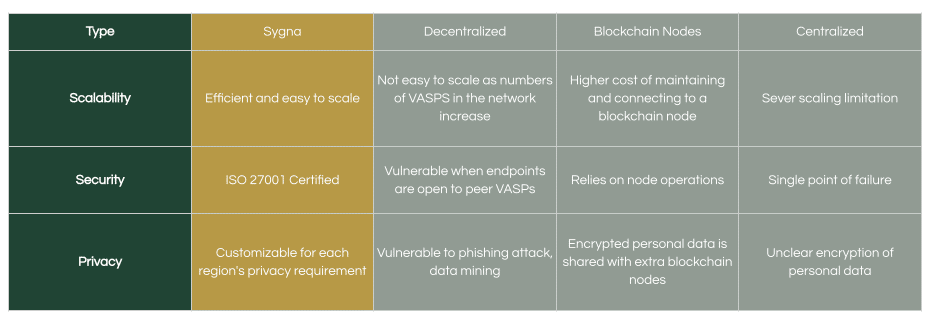
Scalability
Sygna is the most efficient and easy to scale solution, decentralized may suffer extra integrations when new VASP members join the network, blockchain nodes could have slow messaging speed with a higher cost connecting the blockchain nodes, the one server centralized technology has the server scaling limitation.
Security
Sygna is ISO27001 certified by SGS to make sure information security and business continuity, Decentralized technology requires VASPs to open their endpoints to all the other VASPs in the network so that it could be vulnerable to cyber-attacks. Blockchain nodes may have security issues since they operate as one of the substitute nodes, they often do not put a lot of effort into cybersecurity. The centralized technology may suffer a single point of failure.
Privacy
Sygna is highly customizable for each region’s privacy requirements with encryption design. Decentralized technology is vulnerable to phishing attacks and fake transactions for data mining. Blockchain nodes have to share the encrypted personal information with extra blockchain nodes in the synchronizing consensus process. For centralized technology, you should always pay attention to their privacy policy.
Conclusion
In the end, the various Travel Rule solutions may each have their own compelling selling points that will appeal differently to VASPs based on their own requirements.
Compliance officers should also consider the following when evaluating a solution:
- Do you understand the difference between the solutions’ core technologies?
- How important is the centralization/decentralization debate for your organization?
- How strong is the development team on encryption and security?
- Do they have a proven background in fintech security?
- How does the solution protect your data privacy from breaches?
We hope that we’ve provided you with more insights to assist you in your journey to Travel Rule compliance.
If you’d like to know more, please feel free to contact us at services@sygna.io
This session was prepared by Vince Lee, the product manager for CoolBitX on behalf of the Sygna product.
About CoolBitX
CoolBitX is a Taiwan-based blockchain security company that was founded in 2014, we have two main lines of business, the first is a Bluetooth hardware wallet and the second is a technical solution for the travel rule called Sygna Bridge. Thanks for listening. See you in the next 4 lens sessions.


